Fix broken Repository Path in Veeam Scale-Out Backup Repository
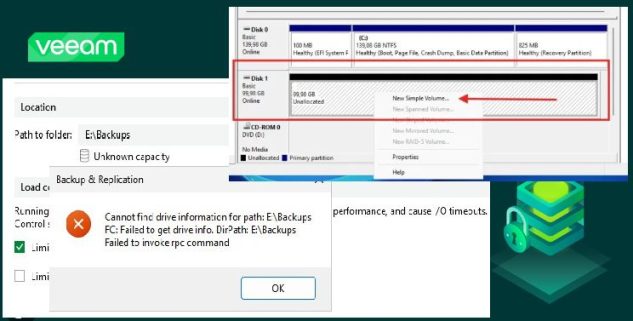
In this article, we shall discuss how to Fix broken Repository Path in Veeam Scale-Out Backup Repository. In the past, we fixed a very similar error but we employed a different approach here “Fix missing path and delete a Veeam Backup Repository“. Here is how to leverage Azure Blob Storage as an Object Storage Repo…
Read More “Fix broken Repository Path in Veeam Scale-Out Backup Repository” »
![Fix Operating System Loader failed signature verification” on Dell Safe BIOS Systems via PXE [Part 3]](https://techdirectarchive.com/wp-content/uploads/2026/05/Fix-Operating-System-Loader-failed-signature-verification-e1778595875592.jpg)
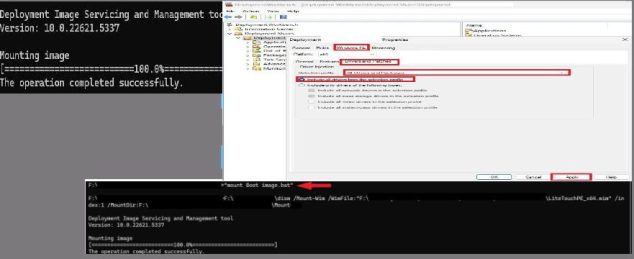
![Update WinPE Boot Images with Windows UEFI CA Certificates [Part 2]](https://techdirectarchive.com/wp-content/uploads/2026/04/how-to-update-WinPE-Boot-Images-with-Windows-UEFI-CA-Cert-e1778595575234.jpg)