What Ransomware Recovery looks like when the clock is ticking

A ransomware recovery strategy is not something you design during an attack. It is something that reveals its true value only when everything else is already failing. In this guide, we shall discuss “What Ransomware Recovery looks like when the clock is ticking”. Please, see How to set up Devolusion Remote Desktop Manager on Windows, and Hardening Your Infrastructure: A Guide to VMware VBS and MS GPO Credential Guard in VBR v13.
In the previous article, we explored attacker thinking and how ransomware families evolved to deliberately target backup systems, as linked below. In this continuation, we move from theory to reality, following the real timeline of a ransomware incident, from the first signs of compromise to full operational recovery.
This is not a checklist. This is what actually happens when a company is under attack. Also, check part 1 from this series, Hacker Thinking in Ransomware Attacks: Backup Is the real Target.
Phase 0 – Before the Attack: When Everything Still Looks Normal
Every ransomware incident starts long before encryption. In many cases, attackers are already inside the environment weeks or even months before anything breaks. Credentials are harvested, backups are mapped, administrative paths are studied, and security gaps are patiently documented.
At this stage, the ransomware recovery strategy is completely invisible, but its quality will define everything that follows.
Organisations that invested early in immutable backups, air-gapped copies, access separation, MFA, and regular restore testing don’t feel safer at this moment. They simply don’t know yet that they are safer. And that difference only becomes obvious later.

Please, see How to fix the Filesystem root is running low on Disk space, and A-Z of XCP-ng and Xen Orchestra setup and VM Creation.
Phase 1 – Detection: The First Signs That Something Is Wrong
Detection rarely starts with a ransom note. More often, it begins with subtle signals:
- unusual authentication attempts,
- backup job failures,
- disabled services,
- sudden changes in retention policies,
- or alerts triggered by unusual activity on protected servers.
At this point, panic is the enemy. The first objective is situational awareness, not reaction. Understanding what is affected, what is still trusted, and whether backup infrastructure is intact becomes critical.
A mature ransomware recovery strategy assumes that production may already be compromised, but backups must still be verifiable and reachable.

Please, see What Happens if You Turn Off Your Computer During an Update, Cybersecurity Tips to Secure Synology NAS, and Hacker Thinking in Ransomware Attacks: Backup Is the real Target.
Phase 2 – Containment: Protecting the Environment Without Destroying Evidence
This phase hides one of the most dangerous traps in incident response. The instinctive reaction is to isolate everything immediately, disconnect networks, power off servers, stop services. While isolation is necessary, doing it blindly can permanently destroy critical forensic evidence.
In some ransomware families, encryption keys or attacker tools may still reside in volatile memory (RAM). Shutting down systems too early can erase information that could later help with decryption analysis, attribution, or legal investigation.
This is where containment must be balanced with preserving volatile data. In certain scenarios, performing a memory dump before shutdown is essential.
From a ransomware recovery strategy perspective, this phase proves that backup professionals must understand more than storage. They must understand incident response realities.

Please, see Google Chrome reports your clock is behind: How to fix clock synchronisation issues in Windows, and “Best Storage for Veeam: Comparing OOTBI by ObjectFirst to VHR“.
Phase 3 – The Moment of Truth: Backup Validation
This is where assumptions die. Backups that “ran successfully” for years suddenly face their real test:
- Are restore points clean?
- Are they immutable?
- Are credentials still valid?
- Can restores be performed without relying on Active Directory?
This phase separates backup existence from backup usability. A strong ransomware recovery strategy includes regular restore testing, isolated validation environments, and confidence that backups are not silently compromised.
This is not about capacity or performance. It is about trust.

Phase 4 – Orchestrating the Comeback
Once recovery starts, the pressure becomes relentless. Business leaders want systems back immediately. Users want access restored. Every minute offline feels like failure. Here lies one of the most painful technical dilemmas in ransomware recovery:
- Speed versus safety.
- Restoring dozens or hundreds of systems quickly is possible. Doing it securely is harder.
Instant recovery technologies can dramatically reduce downtime, but restoring infected systems without verification risks reinfecting the entire environment. Secure restore processes, including malware scanning during recovery, take time! Every backup engineer knows this moment:
“Bring it back now” versus “Bring it back clean.”
A resilient ransomware recovery strategy acknowledges this conflict and defines decision paths before the crisis begins.

Phase 5 – Extended Recovery: The Human Cost of Ransomware
This phase is rarely documented, but everyone who has lived through it remembers it. Recovery does not end when systems come back online. Backup teams work long hours. Engineers sleep next to laptops. Every restore is monitored, every log is reviewed, and every failure is personal.
This is where ransomware becomes more than a technical incident; it becomes an endurance test. A successful ransomware recovery strategy recognises that people are part of the system. Clear roles, escalation paths, and realistic expectations are as important as technology.

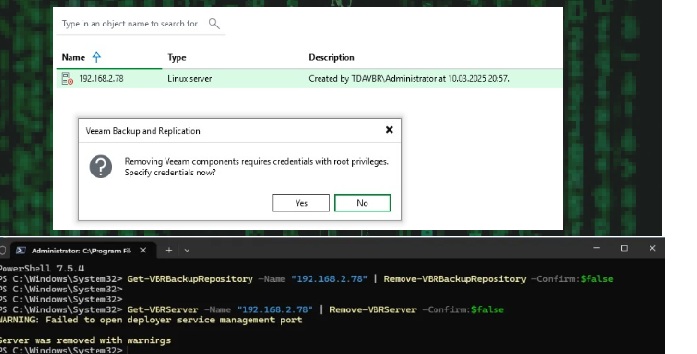
Please, see “Best Storage for Veeam: Comparing OOTBI by ObjectFirst to VHR, and Veeam Host Components: Unable to reinstall Deploy Service SSH.
Phase 6 – Root Cause and Structural Change
Many organisations fail here. Once operations stabilise, there is a temptation to move on. But without understanding how the attacker entered, recovery is incomplete.
Backups often become a crucial forensic asset at this stage. Attackers may have planted backdoors months before encryption. Restoring data without validating historical compromise risks repeating the incident.
Using isolated environments, such as sandboxed recovery labs, allows security teams to investigate malware behaviour safely while production continues to stabilise. A mature ransomware recovery strategy treats recovery not as an end, but as the beginning of structural improvement.

Why Backup Professionals Are the Last Line of Defence
When identity systems fail, when Active Directory is compromised, when endpoints are untrusted, backup infrastructure may be the only remaining reliable system. This reality elevates the role of backup professionals.
They are no longer just administrators of restore points. They become custodians of business survival. That is why modern ransomware recovery strategy discussions must include:
- MFA and emergency access accounts,
- isolation from domain dependencies,
- immutable and air-gapped storage,
- and continuous validation.
Attackers do not win when they encrypt data. They win when recovery fails.
Please see Modern Backup Strategy with Veeam and Wasabi: Truly Immutable and Using IBM Library with Veeam to improve security in your environment.
Final Thoughts
Ransomware defence is not only about prevention. Prevention eventually fails. Resilience is about what happens next. Organisations that survive ransomware incidents do not do so because they were lucky; they survive because their ransomware recovery strategy was designed for the worst day, not the best one.
And when everything else collapses, recovery becomes the last promise the business still believes in.
They win when recovery fails. Veeam professionals make sure it never does.
I hope you found this blog post very useful on “What Ransomware Recovery looks like when the clock is ticking”. Please, feel free to leave a comment below.