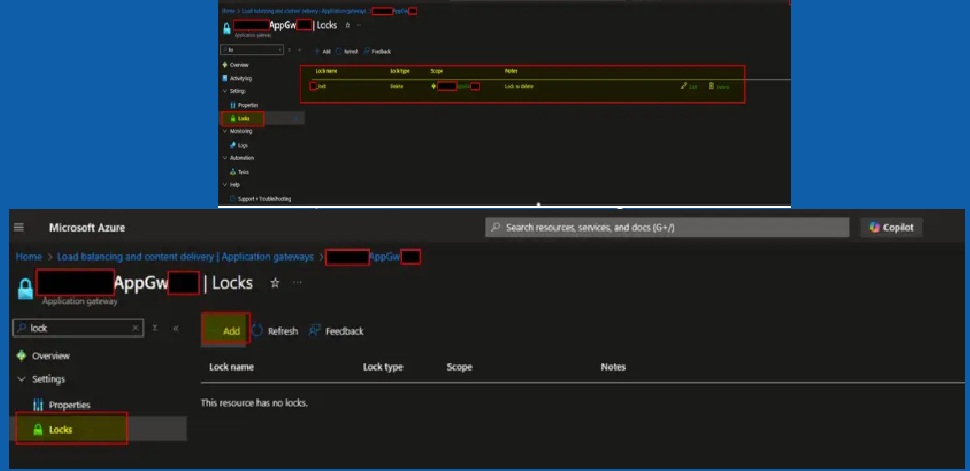
Azure Resource Locks: Protecting Critical Cloud Resources from Accidental and Malicious Deletion

In modern cloud environments, infrastructure protection is no longer optional. Organizations operating on Microsoft Azure must ensure that business-critical workloads, networking components, storage accounts, and security services are protected not only from accidental human errors, but also from unauthorized or malicious actions. In this guide, we shall discuss “Azure Resource Locks: Protect Resources from Accidental…



![How to create a new Azure SQL Database [PaaS]](https://techdirectarchive.com/wp-content/uploads/2025/12/create-a-new-Azure-SQL-Database-1.jpg)
![[AZURE] Security Service Edge (SSE) and Microsoft Entra ID](https://techdirectarchive.com/wp-content/uploads/2025/12/Azure-SASE.jpg)


![[AZURE] Procedure for creating an MSSQL Always On Cluster on Azure](https://techdirectarchive.com/wp-content/uploads/2025/12/MSSQL-Always-On-Cluster-on-Azure-e1765890461654.jpg)