BitLocker is a full volume encryption feature included with Microsoft Windows versions starting with Windows Vista. It is designed to protect data by providing encryption for entire volumes. By default, it uses the AES encryption algorithm in cipher block chaining or XTS mode with a 128-bit or 256-bit key. See this guide for information on Full Disk Encryption with PBA / without PBA, UEFI, Secure Boot, BIOS, File and Directory Encryption, and Container Encryption, how to enable FileVault disk encryption on a Mac device, BitLocker Drive Encryption architecture, and implementation scenarios. and the concept of DriveLock with a focus on encryption.
VMs and Desktops that do not support TPM can still use and benefit from BitLocker, and also have their keys saved to Active Directory, Microsoft Azure, or to a USB stick.BitLocker without TPM
Furthermore, While trying to install Bitlocker Drive Encryption to the C: on my Windows 10 machine. See this guide “how to fix your device cannot use a Trusted Platform Module: Allow BitLocker without a compatible TPM”.
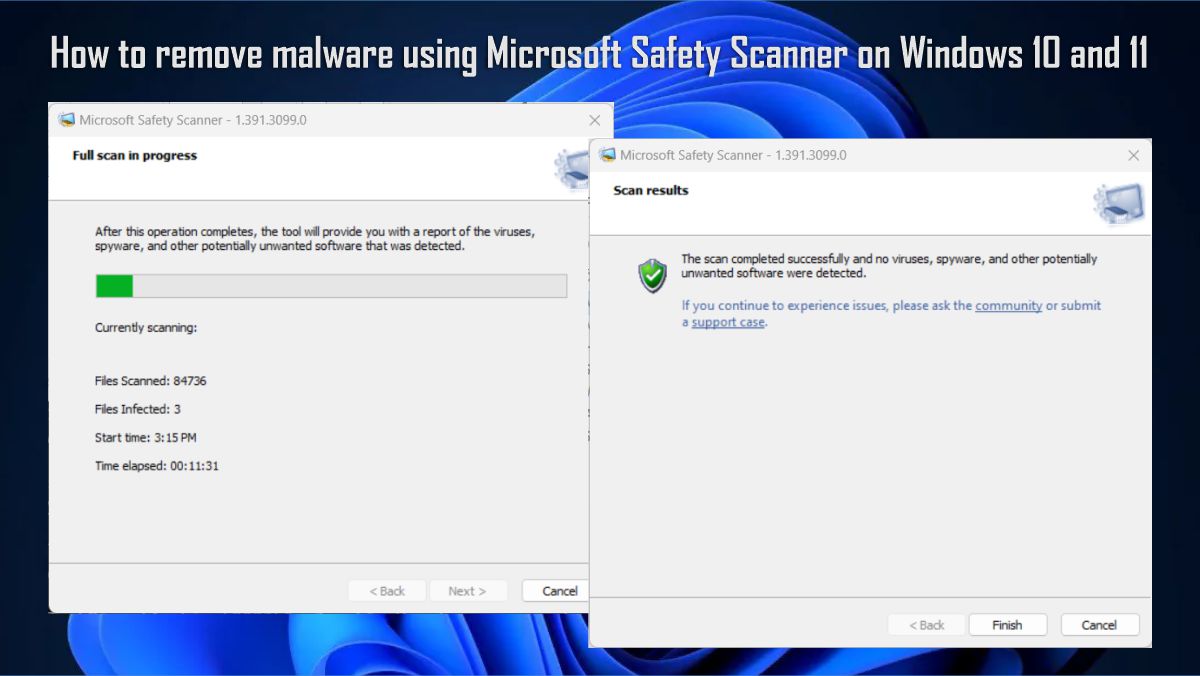
The following error was prompted on my Windows 10 Workstation, as shown in the image below.
Let’s review the key term “TPM” and how to resolve this issue.
However, Trusted Platform Module (TPM) – This chip resides on newer processors with additional security features. With TPM, the encryption key is stored on the chip itself.
Note: If your chip does not support TPM, you can still use BitLocker, then you will have to save (store the keys) in a safe location such as Active Directory, Microsft Azure, or on a USB stick, etc. Kindly follow the procedures listed below to resolve this issue.
Nonetheless, To resolve this error, we must configure the local Group Policy settings to “Allow BitLocker without a compatible TPM.” Nevertheless, For more information on Group Policy, please see the following guides “what is Group Policy Object and how can it be launched“, how to analyze group policies applied to a user and computer account, and for a comprehensive list of articles I have written on GPO, please visit the following link.
Launch Group Policy and enable the following exception
- Using your keyboard ''Windows key+R'' or search for "run"
- Type: gpedit.msc then hit "ok" or press "Enter" on your keyboard
- Expand Administrative Templates then Windows Components
- Bitlocker Drive Encryption then
- Click Operating System Drives as shown below.Therefore, Double-click or right-click “Require additional authentication at startup.”
click Edit and select enabled as shown below.
- Select Enabled and
- Check the box to allow BitLocker without compatible TPM in the Options section.
Note: Most times this option is selected by default.The last steps involve enforcing the settings.
From the Start menu
- Type run or Press Windows Key + R to launch the run wizard
- Type cmd as shown below
- gpforce.exe /update and
- Press Enter.
That is all ;)I hope you found this blog post helpful. If you have any questions, please let me know in the comment session.