Why Software KVMs such as Synergy is replacing Hardware KVMs
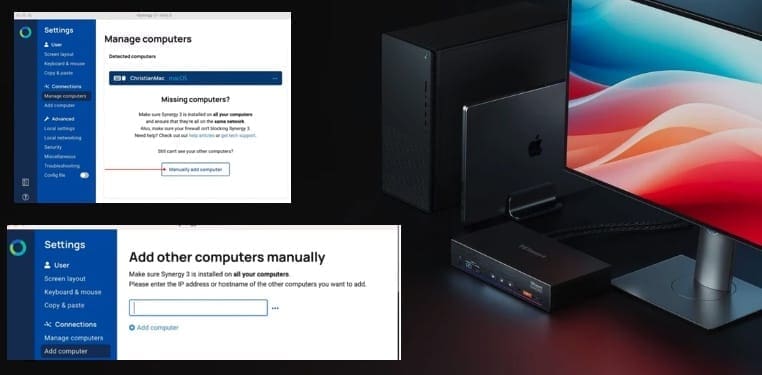
If you have ever found yourself juggling multiple Personal Computers (PCs) at your desk. We bring you a solution that you might not have heard about previously. Synergy is software that lets you use one mouse and keyboard to control multiple PCs across Windows, macOS, and Linux. Just move your cursor between machines like they…
Read More “Why Software KVMs such as Synergy is replacing Hardware KVMs” »