The default configuration of Windows systems prevents the execution of PowerShell scripts by configuring the PowerShell execution policy. This safety feature is implemented to control the conditions under which PowerShell loads configuration files and runs scripts. This feature helps prevent the execution of malicious scripts. Please see “how to set the PowerShell Execution Policy via the Windows Registry settings“. In this article, you will learn how to determine the execution policy configured on a Windows PC.
You may also find this article interesting “How to Set Execution Policy via Windows Settings“. Below are the various values of policies that exist. Also, see how to upgrade Path and In-Place Upgrade for VBR v13 and Known Fixes, how to upgrade Veeam Backup and Replication 12.3, and how to upgrade Veeam Backup and Replication v12.3 to v13 on Windows
What is the PowerShell Execution Policy?
The execution policy isn’t a security system that restricts user actions. For example, users can easily bypass a policy by typing the script contents at the command line when they cannot run a script. Instead, the execution policy helps users set basic rules and prevents them from violating them unintentionally.
The PowerShell Execution Policy determines whether scripts can run on your Windows device. By default, PowerShell sets the execution policy to Restricted, which means that scripts will not run. Windows PowerShell has four different execution policies.
Please see Restrict IP Address Range on Windows PC, Best MacBook you can find in the year 2022, how to Mitigate Windows Print Spooler Remote Code Execution Vulnerability, and How to install and update PowerShell version 7 on Windows and Linux.
Determine the execution policy configured on a Windows PC
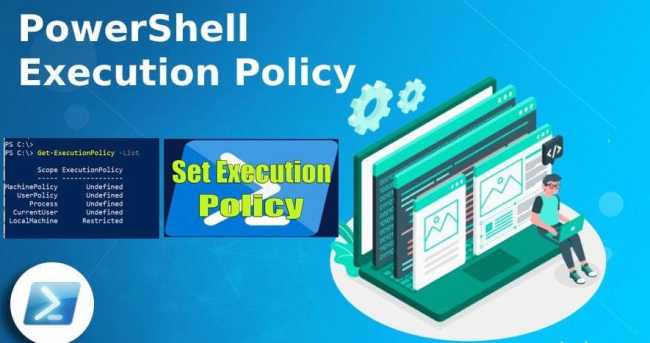
To see the effective execution policy for your PowerShell, first, open an elevated Powershell window, accept the UAC, and enter the below Powershell command.
To reveal the effective execution policy for your PowerShell session use “Get-ExecutionPolicy“. Today’s precarious security environment allows attackers to take advantage of newly discovered vulnerabilities. As depicted below, the default policy is set to “unrestricted.”
The effective execution policy is determined by execution policies that are set by “Set-ExecutionPolicy” and Group Policy settings. See this guide for more information on “how to set Execution Policy via Windows PowerShell“
Get-ExecutionPolicy
To display the execution policies for each scope in the order of precedence, use “Get-ExecutionPolicy -List“.
FAQs
The PowerShell Execution Policy is designed to control the security levels for script execution. It helps prevent the execution of malicious scripts and ensures a secure environment.
PowerShell provides several execution policy levels, including Restricted, AllSigned, RemoteSigned, Unrestricted, and Bypass. Each level offers a different degree of script execution control.
You can check the current PowerShell Execution Policy by using the Get-ExecutionPolicy cmdlet. This command will display the current policy setting for the session.
To change the PowerShell Execution Policy, use the Set-ExecutionPolicy cmdlet followed by the desired policy level. You may need to run PowerShell with administrator privileges to make this change.
I hope you found this blog post helpful on how to determine the execution policy configured on Windows PC. If you have any questions, please let me know in the comment session.