Veeam Agent for Microsoft Windows is a key component of Veeam Backup & Replication expanding its capabilities beyond virtual to protect Physical and Cloud workloads running Microsoft Windows. In this short guide, we shall discuss “CVE-2022-26503 Veeam Agent for Microsoft Windows Vulnerability”. Kindly refer to these related guide how to Set up Veeam Backup for Microsoft Azure, how to uninstall Veeam Backup and Replication from your server, and how to Install Veeam Backup And Replication With Dedicated SQL Server.
Present issue
The Vulnerability (CVE-2022-26503) in Veeam Agent for Microsoft Windows allows local privilege escalation. An attacker who successfully exploited this vulnerability could run arbitrary code with LOCAL SYSTEM privileges. It currently has a severity of High assigned and classified with the CVSS v3 score “7.8”.
Also, see “The push installation of the agent failed for the computer – Error message (67) The network cannot be found“, and “Veeam Agent Vulnerability: Fix Veeam Agent vulnerability for Microsoft Windows“.
Cause of Veeam Agent for Microsoft Windows Vulnerability
Veeam Agent for Microsoft Windows uses Microsoft .NET data serialization mechanisms. A local user may send malicious code to the network port opened by the Veeam Agent for Windows Service (TCP 9395 by default). Which will not be deserialized properly.
Note: There isn’t a workaround for the Veeam Agent vulnerability similar to Veeam Backup & Replication critical vulnerability.
You will need to find a maintenance window to have the Veeam Agent upgraded on all affected Veeam Agent clients to remediate the vulnerability.
Please, see Backup Mac with Veeam Agent for Mac to Synology DS923+ NAS, how to upgrade Veeam Backup and Replication 12.3, and how to perform vulnerability scan on Microsoft SQL Server.
The solution to resolving CVE-2022-26503
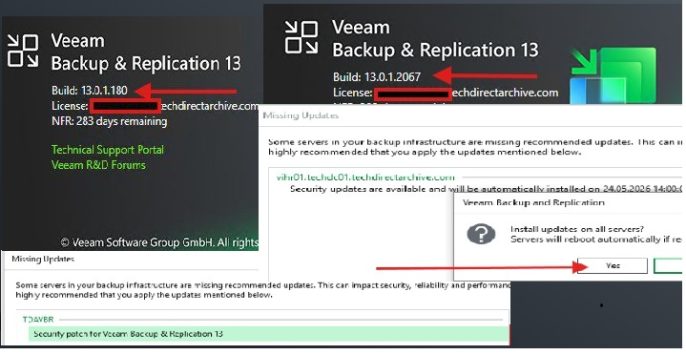
This vulnerability is fixed in the following Veeam Agent for Microsoft Windows patched releases. Which are: 5 (build 5.0.3.4708), and 4 (build 4.0.2.2208)
Take note of the following guidance from Veeam on remediating your Veeam Agents:
- For the standalone version of Veeam Agent for Microsoft Windows (not managed by Veeam Backup & Replication).
The patched release will need to be manually installed on each Veeam Agent machine. If your Veeam Agents are managed by Veeam Backup & Replication. You can upgrade your Veeam Agents from the Veeam Backup & Replication Console after installing the cumulative Veeam Backup & Replication patches. Ideally, install the remediated version of VBR that fixes the new critical vulnerabilities. And then upgrade your Veeam Agents from there.You can also upgrade the Agents automatically if the “auto-update backup agent” setting is enabled.
Note: If you are using a version of Veeam Agent for Microsoft Windows prior to 4. Please upgrade to a supported version.
I hope you found this blog post on “CVE-2022-26503 Veeam Agent for Microsoft Windows Vulnerability” helpful. If you have any questions, please let me know in the comment session.