Best Storage for Veeam: Comparing OOTBI by ObjectFirst to VHR

In this article, we shall discuss the “Best Storage for Veeam: Comparing OOTBI by ObjectFirst to VHR and why physical security is necessary to Protect OOTBI”. Out-of-the-Box Immutability (OOTBI) by ObjectFirst and Veeam Hardened Repository (VHR) are closely intertwined and designed specifically for Veeam Backup and Replication at the point of writing this article. Please see Create a bootable USB on Mac: Proxmox VE Setup, and how to Upgrade Windows Admin Center 2306 – 2311: Run WACmg v240.
Before diving into this topic, it is vital to discuss what a backup repository is. Backup repositories are the destination of backup and backup copy jobs in Veeam Backup and Replication. and can be used to store configuration backups of remote Veeam Backup servers.
Also, see what is the difference between iDRAC, IPMI, and ILO, and how to Generate CSR and Request a Certificate from Herica CA. Here is how to configure WebLAPS to manage Microsoft LAPS.
Veeam Hardened Repository (VHR)
The Veeam Hardened Repository (VHR) provides a secure mechanism to protect and backup your data from loss as a result of malware activity or unplanned actions. This therefore makes it a preferred choice for Veeam enterprise customers seeking advanced ransomware protection and compliance-ready backup storage.
By leveraging Linux XFS with immutability, VHR ensures that backup data remains tamper-proof, undeletable, and resilient against cyber threats, even if an attacker gains administrative access.
With strict access controls and sudo rights automatically stripped. VHR prevents unauthorized modifications while integrating seamlessly into Veeam’s backup and recovery ecosystem. This makes it a powerful, flexible, and cost-effective option for organizations prioritizing data integrity, regulatory compliance, and long-term backup security.
Please see DSM Security: How to Protect Synology DS923+ NAS, Cybersecurity Tips to Secure Synology NAS against Ransomware, and Sign-in options for Windows: Ditch Password for Enhanced Security.
Out-of-the-Box Immutability (OOTBI)
On the other hand, Object First’s Out-of-the-Box Immutability (OOTBI) delivers secure, simple, and powerful backup storage, purpose-built for Veeam customers. In my lab test, I racked, stacked, and powered the appliance in less than 15 minutes. This, therefore confirms it is a ,fast and hassle-free deployment.

With zero trust and data security principles with built-in immutability, Ootbi helps drastically reduce the risk of ransomware affecting backup data.
Please, see how to upgrade Veeam Backup and Replication 12.3, how to install Veeam Backup Console on a Jump Server, and how to fix missing path and delete a Veeam Backup Repository.
Comparing OOTBI to VHR?
When comparing Veeam Hardened Repository (VHR) and Object First Out-of-the-Box Immutability (OOTBI). The key distinction lies in ownership and required expertise. This can be likened to the difference between WordPress.org (self-hosted, hands-on) and WordPress.com (managed, secure by default).
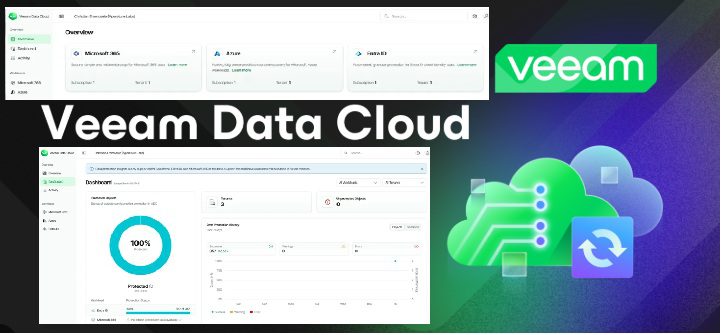
With VHR, you have to manage, search and apply OS updates and security patches, mitigate threats in your enviornment yourself, etc. But, for OOTBI, when there is an available update, you will be prompted to apply this over the dashboard. Thereby mitigating the impact of zero-day vulnerabilities and exploits. Please see how to update the Object First OOTBI Cluster.
OOTBI has an integrated dashboards, ability to adds nodes later on etc. OOTBI is built for simplicity and security, eliminating common attack vectors:
- Immutability is enforced by default. Here, backup admins cannot disable or alter retention.
- Pre-configured security removes the risk of misconfiguration.
- Plug-and-play deployment requires minimal setup. Please see how to Configure Object First OOTBI Appliance.
Note: With OOTBI, even privileged admins cannot modify or delete immutable backups. Also, with VHR, when Immuntability is configured, the sudo right is stripped off. The required expertize is needed.
Note: For VHR, it leverages Linux XFS with immutability (chattr +i) to lock backup files. To prevent any modifications, Veeam automatically removes sudo privileges from the user managing the repository. This ensures that even root cannot easily delete or modify immutable backups as well (unless the immutability period expires).
How is OOTBI more Resilient
As discussed above, the only evident difference is that VHR requires the desired Linux skills for the initial configuration and subsequent maintenance. Whereas OOTBI enforces immutability by design with no technical expertise needed.
Then, why is OOTBI more resilient? OOTBI is a self-contained, pre-hardened and independent of external OS administration.
OOTBI is inherently separated from the Veeam Backup & Replication server due to its Zero Trust Data Recovery (ZTDR) architecture and secure appliance form factor. This separation ensures strong segmentation between the Backup Software and Backup Storage layers. Thereby, enhancing ransomware resilience by preventing lateral movement and unauthorized access between the two layers. This design locks down backup data and minimizes attack surfaces, ensuring maximum protection against threats.
Zero Trust replaces outdated perimeter security models, which no longer protect modern hybrid cloud, mobile, and remote work environments. Governments, mid-sized businesses, and large enterprises especially those in banking, healthcare, technology, and manufacturing are rapidly adopting Zero Trust as the new IT security standard. Please see Demystifying Zero Trust with Veeam: Design your Architecture
Independent third-party testing and continuous validation ensure that our hardened object storage appliance provides an impenetrable, ransomware-proof target for Veeam backup data even when the OS is compromised. With zero access to the operating system, it eliminates attack vectors, reinforcing data security and integrity. Also, OOTBI is
- Unaffected by OS reinstallation: Immutable data remains intact and this applies for VHR with the latest repair mode as well.
- Resistant to ransomware: Cannot be deleted or encrypted, even if the OS is compromised.
- Simplified for compliance: Ensures regulatory adherence without complex configurations.

VHR
In contrast, VHR relies on correct user configurations, keeps them secure and updated, and performs to expectation. This is not practical for most Veeam admins in the mid-enterprise to take on in addition to their day-to-day responsibilities.
Also, VHR could be vulnerable if an administrator unintentionally weakens security settings. Other than this, VHRs are by far the best choice as compared to DAS, Dedupe Appliance in the diagram above. See the image below for more information.

None of these options fulfils the Veeam admin’s need for a simultaneously secure, simple, and powerful solution. Without further ado, get on OOTBI appliance today. This brings us to discussing OOTBI extensively.
Here is how to integrate ObjectFirst OOTBI Appliance with VBR, and how to Achieve 3-2-1 rule with SOBR on Synology or OOTBI and Wasabi. Also, see how to create Synology Snapshot Replication.
How does OOTBI Stand out from other Object Storage vendors?
Most object storage vendors originally designed their on-premises appliances for distributed, web-scale containerised enterprise applications. They later optimized their S3 implementations to handle small data writes across many containers.
Later, these systems were retrofitted for data backup. But kept unnecessary features and complexity. As a result, these systems were never purpose-built for backup workloads.
Out-of-the-box immutability (OOTBI) takes a different approach. It was specifically designed for Veeam data backup, ensuring efficient storage of large datasets in a single location for fast, reliable access. That’s why OOTBI’s object storage is both simple and powerful, making it the ideal choice for Veeam backup data.

Here is how to create a Tailscale VPN connection to Synology NAS, and Object First OOTBI Appliance Unboxing and Quick Setup for some additional physical security tips.
Physical and Hardware Control – Disable IPMI
The IPMI is a standardised interface defined by the Intelligent Platform Management Interface Forum (IPMI Forum). IPMI is not tied to a specific vendor but is a standardized protocol that various server manufacturers implement in their hardware.
Physical security is necessary to protect Out-of-the-Box Immutability (OOTBI) because even the strongest software-based controls (such as S3 Object Lock in Compliance Mode) can be bypassed if an attacker gains physical access to the underlying hardware.
The hardware stack consists of multiple layers, each playing a role in system operation. If an attacker gains control at a lower layer, they can manipulate higher layers, including the application layer.
IPMI (Intelligent Platform Management Interface) can pose a significant risk to OOTBI if not disabled after the initial setup. Even though OOTBI ensures software-level immutability (such as S3 Object Lock in Compliance Mode), IPMI provides low-level remote management access to hardware, which could be exploited to bypass logical protections.
Protecting the underlying physical server components from unauthorised access is also paramount to protecting remote access. Below are some reasons to disable IPMI.
- Prevents Unauthorized Remote Access: Attackers often exploit IPMI vulnerabilities to gain low-level control over a server.
- Reduces the Risk of Firmware Attacks: IPMI can be used to modify BIOS/firmware, leading to persistent backdoors.
- Limits Insider Threats: Disabling IPMI ensures that even disgruntled users with physical access to the data center cannot use it to take remote control. This will also help prevent forced shutdowns and reboots.
Note: A forced reboot with malicious boot media could introduce vulnerabilities that weaken OOTBI protections. IPMI can be used to mount virtual media remotely, allowing attackers to install unauthorized software or alter disk partitions. This could enable an attacker to wipe or alter data storage settings, potentially leading to data loss.
Please see how to Harden your Veeam Backup Server with Microsoft AppLocker, how to Upgrade Veeam Backup and Replication to version 12.2, and how to Backup Mac with Veeam Agent for Mac to Synology DS923+ NAS.
Mitigation IPMI Threats
While OOTBI ensures software-level immutability, IPMI can be a backdoor for attackers to physically disrupt, reconfigure, or compromise storage at the hardware level. Securing IPMI access is critical to maintaining true immutability and preventing attacks that could undermine data integrity.
As you can see below, Object First highly recommends having the IPMI access disabled. For other security best practices, see OOTBI Security Best Practices: Enable Honeypot on Object First.

To disable IPMI, please login to the ObjectFirst Management Console, click on Settings and select Network. Under the “Network interfaces”, please select the checkbox “Disable” and click on “Apply Changes”.

Please see how to integrate ObjectFirst OOTBI Appliance with VBR, how to create Synology Snapshot Replication, and Single App Kiosk Mode Configuration using MDM Bridge WMI Provider.
I hope you found this article useful on “Best Storage for Veeam: Comparing OOTBI by ObjectFirst to VHR – Why physical security is necessary to Protect OOTBI”. Please feel free to leave a comment below.