Object First OOTBI (Out-of-the-Box Immutability) is a purpose-built, secure, and immutable backup storage solution engineered specifically for Veeam Backup & Replication. This guide discusses the “Understanding User Roles & Access Control in Object First OOTBI”. Please, see How to Configure Object First OOTBI Appliance, how to update Object First OOTBI Cluster, and Object First OOTBI Appliance Unboxing and Quick Setup.
Table of contents
Object First “OOTBI” was designed by the founder of Veeam, and it eliminates the complexity associated with traditional backup storage by offering an appliance that you can deploy, configure, and integrate with Veeam in minutes. Its architecture prioritizes immutability, ensuring that backup data remains tamper-proof, ransomware-resistant, and always recoverable.
OOTBI leverages object storage technology optimized for Veeam. This enables organizations to store backups directly and securely without managing additional infrastructure layers. By combining storage performance, immutability, and simplicity. OOTBI helps IT teams achieve reliable data protection while reducing operational overhead.
Also, see how to perform Offline and Online Update for Object First Out-of-the-Box Cluster, how to integrate ObjectFirst OOTBI Appliance with VBR. Here is how to create a backup job for Proxmox VMs using VBR.
Role-Based Access Control (RBAC) in Object First OOTBI
However, security in a backup environment goes beyond just immutable storage. It also depends on who has access and what they can do within the system. This is where user roles and permissions play a critical role.
Implementing Role-Based Access Control (RBAC) in Object First OOTBI allows administrators to assign specific privileges to users based on their job responsibilities.
By doing so, organizations can enforce the principle of least privilege, ensuring that each user only performs actions necessary for their role. For example, a system administrator may require OOTBI Cluster access, while an auditor only needs read-only visibility.
This granular control minimizes the risk of accidental or malicious changes, safeguards critical backup data. This further supports compliance with standards such as GDPR, ISO 27001, and NIST. It also simplifies auditing and accountability by clearly defining who can access or modify sensitive configurations.
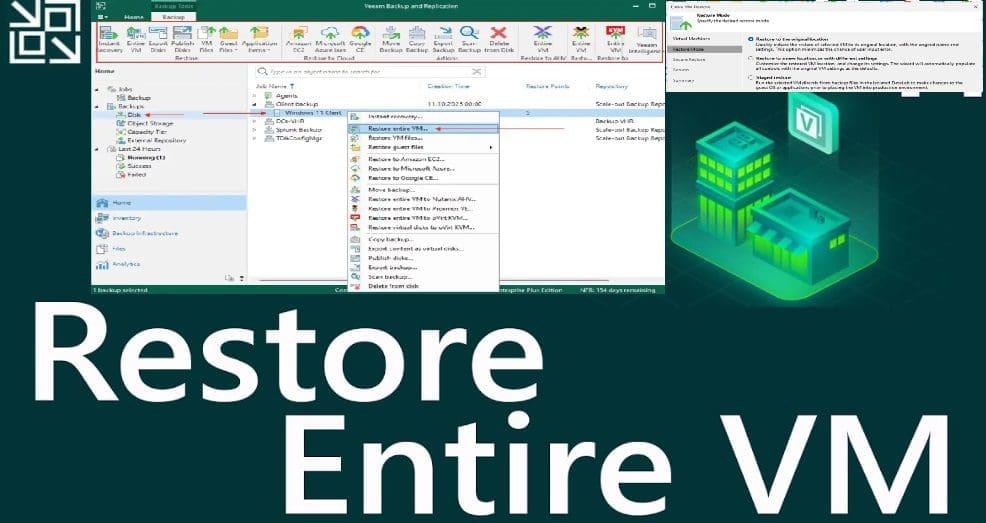
Please, see how to Migrate Windows Servers from Hyper V to Proxmox Correctly, and how to Restore VM to Original location using Veeam Entire VM restore.
OOTBI User Roles
When you create a new user in OOTBI, the setup wizard prompts you to assign a role that defines their level of access. The image below table discusses the roles and use-cases. In essence, OOTBI not only protects your backups from external threats but also fortifies them internally through intelligent access management.
By properly assigning user roles, you strengthen the overall security posture of your backup storage infrastructure and maintain confidence that your data remains both secure and compliant.
| Role | Description | Best Use Case |
|---|---|---|
| Administrator | Full access to the OOTBI cluster | For system admins managing configuration and upgrades |
| Hardware Operator | Admin without access to S3/IAM | For operators handling hardware but not data policies |
| Read-only | View-only access to the Web Console | For auditors or compliance officers |
| Power REST Manager | Manage nodes and power operations via API | For automation or DevOps engineers |
| Bucket Manager | Manage S3 buckets only | For storage admins managing backup repositories |
Please, see MFA on Root Account: Create a User on AWS and Register MFA, Deep Dive into Protecting AWS EC2, RDS Instances and VPC, and Creating IAM Users, Adding MFA and Policies on AWS.
How to create a User on OOTBI
To do this, from the Object First OOTBI dashboard, click on Users. In this window, click on create user as shown below. Enter the name, password etc., and click Next.

Select the appropriate user role. See how to Migrate Microsoft Enterprise Root Certification Authority and Forest Domain Domain on Azure

In my case, I will select Read-Only user role and click on Next to continue.
The Read-only role allows users to log into the Web Console with view-only access. They can monitor system status, storage usage, and configuration details but cannot modify or delete any settings. This role is ideal for auditors, compliance officers, or managers who need visibility into the system for reporting or verification purposes. By limiting their access to viewing only, you ensure transparency without compromising operational control.

On the summary window, click on create as shown below.

You will be prompted to enter your password to confirm action.

If you have Multi-Factor authentication enabled, you will be prompted to enter the 2FA code as shown below. For more information on this, see ‘OOTBI Security Best Practices: Enable Honeypot on Object First“.

As you can see, we have successfully created a new user with the role “read-only” o access the OOTBI cluster.

Conclusion
By assigning distinct roles, you enforce separation of duties. A core security principle that prevents any single user from having unchecked control. This structure not only reduces the chance of human error or malicious actions. But also strengthens compliance alignment with enterprise governance frameworks like COBIT, ISO 27001, and NIST etc.
Furthermore, role-based access helps streamline daily operations. Administrators can focus on core infrastructure management, while auditors and operators perform their tasks without overlapping responsibilities. The result is a more secure, efficient, and accountable backup environment.
I hope you found this article on “Understanding User Roles & Access Control in Object First OOTBI” very useful. Please, feel free to leave a comment below.