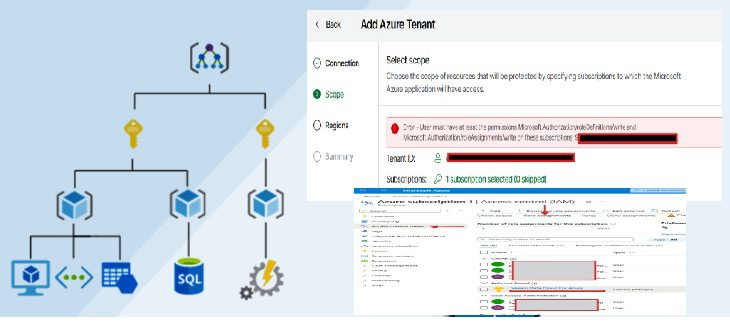
In modern cloud environments, infrastructure protection is no longer optional. Organizations operating on Microsoft Azure must ensure that business-critical workloads, networking components, storage accounts, and security services are protected not only from accidental human errors, but also from unauthorized or malicious actions. In this guide, we shall discuss “Azure Resource Locks: Protect Resources from Accidental deletion”. Please see How to Add a Delete Lock on Azure Resources, and Fix MDT accidental OS deletion.
One of the most effective governance mechanisms available in Azure is the Azure Resource Lock feature. Azure Resource Locks provide a native protection layer that prevents users from deleting or modifying resources, even when they have elevated permissions.
Azure Resource Manager (ARM) governance capabilities include these locks, and organizations commonly adopt them in enterprise landing zones, production subscriptions, and regulated environments.
Also, see How to disable automatic screen lock in Ubuntu Linux, how to Delete or Rename and Create a Protected Organisation Unit in AD, and Read-only Files: Saving Files in VIM Editor on Linux/Unix-like OS.
Why Azure Resource Locks Matter
Cloud administrators frequently face operational risks caused by:
- Accidental deletion of production resources
- Misconfigured automation pipelines
- Unauthorized infrastructure modifications
- Insider threats
- Incomplete governance enforcement
- Human error during maintenance activities
A single accidental deletion of a virtual network, Key Vault, storage account, or production database can result in downtime, data loss, and compliance violations.
Azure Resource Locks mitigate these risks by enforcing protection at the Azure Resource Manager control plane level. Once you apply a lock, Azure blocks the operation regardless of the permissions assigned through Azure RBAC.
This makes Resource Locks a critical component in enterprise-grade Azure governance strategies.
Please see Update WinPE Boot Images with Windows UEFI CA Certificates [Part 2], how to perform Tape Drive Cleaning in Practice, and Active Directory Vulnerability Assessment with Purple Knight: Domain Controller Owner Is Not an Administrator.
Types of Azure Resource Locks
Azure provides two lock levels:
1: CanNotDelete Lock
The CanNotDelete lock prevents a resource from being deleted while still allowing authorized users to modify it. Typical use cases include:
- Production virtual machines
- Critical storage accounts
- Shared networking infrastructure
- Backup vaults
- Domain controllers
- Key Vault instances
This lock is ideal when operational changes are still required but deletion must be strictly prevented.
2. ReadOnly Lock
The ReadOnly lock prevents both deletion and modification of a resource. When this lock is applied:
- Resources can still be viewed
- Configuration changes are blocked
- Update operations fail
- Delete operations fail
A ReadOnly lock effectively limits interactions to read operations only, similar to assigning Reader-level behavior across all users. This model is particularly useful for:
- Security baselines
- Compliance-sensitive environments
- Immutable infrastructure patterns
- Golden configuration templates
Please see Fix Operating System Loader failed signature verification” on Dell Safe BIOS Systems via PXE [Part 3], and how to protect Microsoft 365 beyond native limits with VDC [Part 1].
Lock Inheritance Model
One of the most important concepts in Azure Resource Locks is inheritance. Locks applied at a higher scope automatically propagate to child resources. Azure supports locks at three levels:
- Subscription
- Resource Group
- Individual Resource
For example:
- A lock applied to a Resource Group automatically protects all resources inside that group
- A lock applied at Subscription level affects every contained Resource Group and resource
This hierarchical inheritance guarantees consistent governance across large-scale Azure environments.
Choose the resource you want to protect. In this example, I will apply a lock on delete to the ‘Application Gateway’ resource:

In the left-hand panel, look for ‘Lock’ and select “Add”:

Fill in the forms and select the setting that suits your needs: ‘Lock on delete’ or ‘Read Only’:

You have created your resource lock:

I hope you found this article on “Azure Resource Locks: Protect Resources from Accidental deletion” very useful. Please feel free to leave a comment below.